Is Your Business Balancing API Productivity Gains with Risk Mitigation?
APIs are a critical component of any digital business, sharing information between various software solutions and streamlining and improving business productivity through system integration. They allow modularity in development projects, increase the scalability of the business and in theory should enhance your software security. API security breaches have become increasingly common in recent years, with… Continue reading Is Your Business Balancing API Productivity Gains with Risk Mitigation?
Black Box Penetration Testing
Penetration testing – or pen-testing as we colloquially call it – is a crucial component to a robust security programme in any organisation. As management, it’s critical you understand where pen-testing fits into your programme and what it can do for your organisation. Equally important is what it can’t do, and how the different “flavours”… Continue reading Black Box Penetration Testing
When it all goes wrong on AWS – how an SSRF can lead to full control of your EC2 infrastructure
AWS is an incredibly powerful cloud platform that enables businesses to quickly and efficiently deploy a wide range of software and services to end users. This feature-rich environment does of course increase the attack surface that bad actors have to exploit, especially when combined with lax configurations and poorly designed APIs. In this blog post,… Continue reading When it all goes wrong on AWS – how an SSRF can lead to full control of your EC2 infrastructure
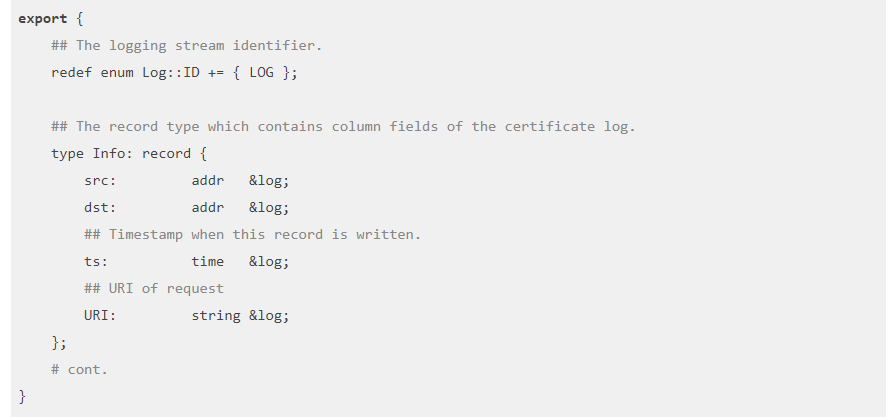
Using Zeek to detect exploitation of Citrix CVE-2019-19781
Using the tool Zeek, formally known as bro, is a high-level packet analysis program. It originally began development in the 1990s and has a long history. It does not directly intercept or modify traffic, rather it passively observes it and creates high-level network logs. It can be used in conjunction with a SIEM to allow… Continue reading Using Zeek to detect exploitation of Citrix CVE-2019-19781
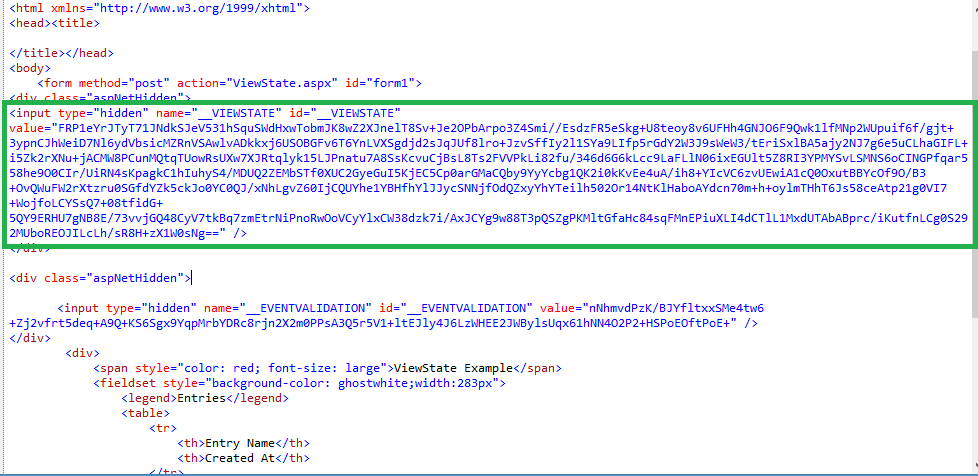
Exploiting ASP.NET ViewState Misconfigurations for Remote Code Execution
This post explores how an ASP.NET project incorrectly disclosing its web.config containing static keys allows for remote code execution. The common cases for exploiting this vulnerability would be if the web application has published it’s static machine keys to GitHub, such as with the example project for this post (https://github.com/ozajay0207/EGVC) or if the application has… Continue reading Exploiting ASP.NET ViewState Misconfigurations for Remote Code Execution