A Strategic Approach to Business Disaster Recovery
Planning for Disaster Recovery Disaster recovery is a critical component of business continuity, especially for medium to large enterprises that rely heavily on digital infrastructure, or use their digital infrastructure for any business operations. Cyber threats, natural disasters, hardware failures, and human errors can severely disrupt operations, resulting in financial losses and reputational damage. To… Continue reading A Strategic Approach to Business Disaster Recovery
Government Initiatives and Sanctions: Strengthening Cyber Security in Australia
The Australian Federal Government has launched several initiatives to combat cybercrime, with a particular focus on ransomware attacks. The introduction of new regulations, sanctions on cybercriminal groups, and the development of practical resources like the Ransomware Playbook signal a firm stance against digital threats. For companies affected by cyberattacks, cyber security service providers like Red… Continue reading Government Initiatives and Sanctions: Strengthening Cyber Security in Australia
Infostealers – The Risk Continues to Grow
Over recent years, Info stealer malware, also called infostealers, has grown as a formidable adversary for businesses worldwide, particularly in Australia. These malicious software programs are designed to infiltrate networks, stealthily collect sensitive data, and transfer it to cybercriminals who use it for financial gain, espionage, or other illicit activities. As Australian enterprises increasingly rely… Continue reading Infostealers – The Risk Continues to Grow
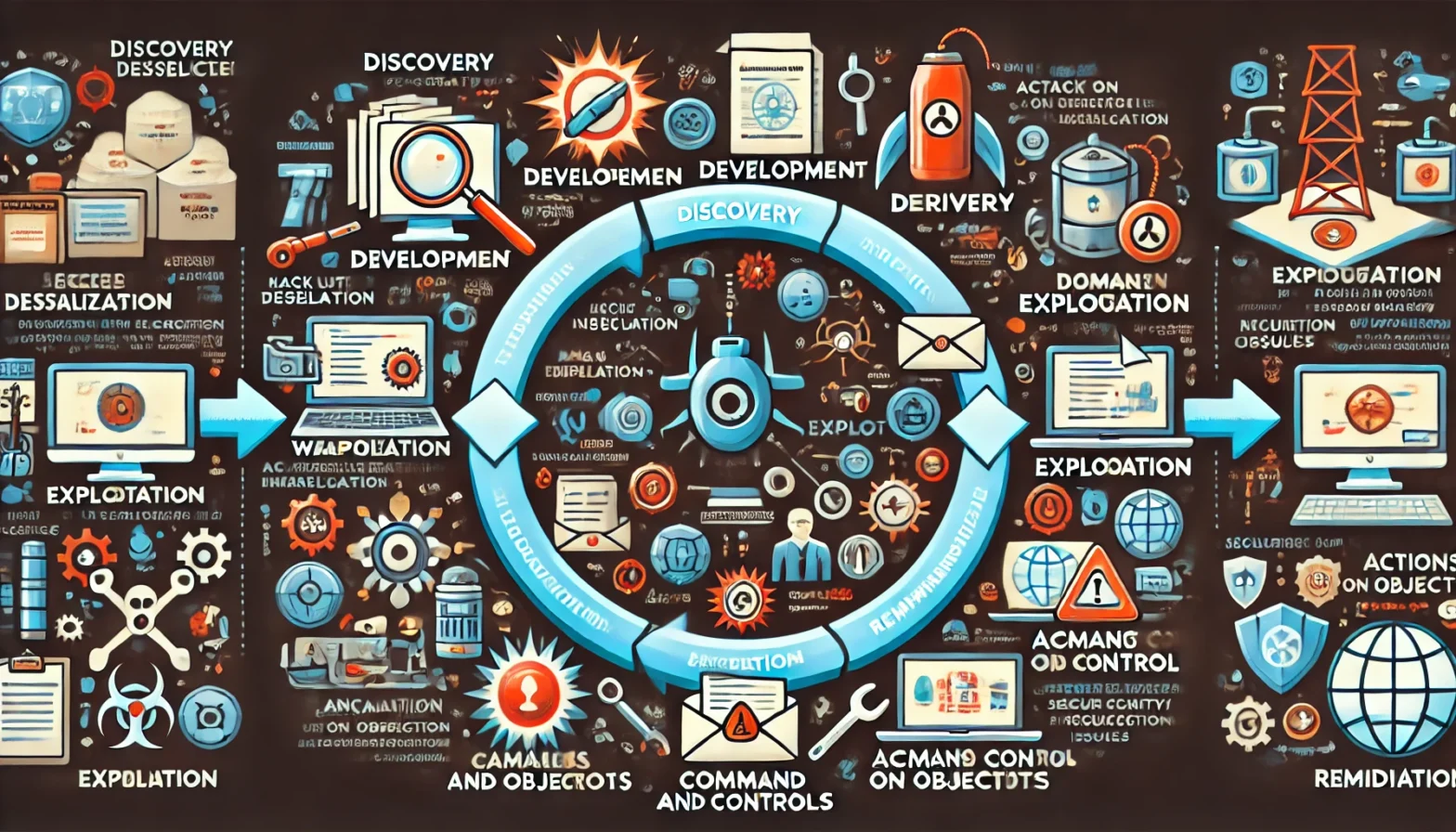
Building an Effective Cyber Security Plan
Building an effective cyber security strategy is no longer optional for medium to large businesses in today’s digital world. Businesses face an increasing threat to their systems, their data and criminal behaviour. Australian companies face not just local threats but a global spectrum of cyber risks, including data breaches, malware, ransomware, and phishing attacks. A… Continue reading Building an Effective Cyber Security Plan
Understanding Common Code Programming Issues Leading to Security Breaches
A great deal of focus when thinking about and or discussing security breaches is generally directed to issues with networks and or social engineering. In reality, many of these breaches stem from common issues in code writing. This blog explores different types of breaches, the potential damage each can inflict, and preventive measures that can… Continue reading Understanding Common Code Programming Issues Leading to Security Breaches
Embracing Zero Trust Security: A Strategic Imperative for Modern Businesses
Cyber threats are continuing to evolve, grow in sophistication and be more pervasive, causing traditional security measures to be no longer sufficient. This inadequacy has paved the way for the adoption of Zero Trust security strategies, a paradigm shift in how security is approached and implemented within organisations. Organisational adoption of Zero Trust security frameworks… Continue reading Embracing Zero Trust Security: A Strategic Imperative for Modern Businesses
The Rise of Info Stealer Malware: A Growing Threat to Businesses
Stealer malware, or information-stealing malware, is a type of malicious software designed to gather sensitive information typically targeting personal, financial, or business-related data. The data collected could include passwords, financial information, corporate data, and personal identification details. Once installed, this malware operates discreetly, often without triggering any noticeable alarms, making it particularly dangerous. The functionality… Continue reading The Rise of Info Stealer Malware: A Growing Threat to Businesses
Will AI Kill the Pen Testing Star
Those who use the different AI support technology available, are seeing a trend, that the results, generally speaking, produced by the tools are getting better every month. There is still the old computing issue of garbage in, garbage out, but as we learn to better seed the bots and the bots learn what data we… Continue reading Will AI Kill the Pen Testing Star
How AI is Impacting Cybersecurity and Penetration Testing
In the era of rapid technological advancement, the proliferation of AI platforms is revolutionising the way we interact with digital information, enhancing productivity, and streamlining decision-making processes. However, this same technology, designed to simplify and enrich our lives, is being weaponized by hackers and bad actors. These individuals exploit the capabilities of AI to orchestrate… Continue reading How AI is Impacting Cybersecurity and Penetration Testing
The Impact of Cybersecurity Breaches on Australian Businesses in 2023
In the digital era, cybersecurity breaches are a critical concern globally, and Australia is no exception. With the increasing dependency on digital platforms, Australian businesses face significant challenges in safeguarding data. The Office of the Australian Information Commissioner (OAIC) plays a pivotal role in monitoring these breaches, providing valuable insights into the cybersecurity landscape in… Continue reading The Impact of Cybersecurity Breaches on Australian Businesses in 2023