How AI Chatbots can Expedite Penetration Testing Service Delivery
ChatGPT is an artificial intelligence (AI) language model developed by OpenAI that is capable of generating human-like responses to natural language input. It is based on the Generative Pre-trained Transformer (GPT) architecture and has been trained on a vast amount of text data, enabling it to understand and generate coherent and relevant responses to a… Continue reading How AI Chatbots can Expedite Penetration Testing Service Delivery
Using Mimikatz
OverPass-the-Hash Mimikatz can perform the well-known operation “OverPass-The-Hash” to run a process under the security context of another account’s credentials. This is extremely powerful and should not be underestimated. Behind the scenes, Mimikatz requests a Kerberos ticket from the domain controller using the NTLM hash provided. The Kerberos ticket allows authentication to Kerberos services within… Continue reading Using Mimikatz
Penetration Testing Frequently Asked Questions
When is penetration testing required? You have developed an application (in-house or outsourced), purchased an application (commercial off the shelf product), or purchased a software as a service (SaaS) and have concerns or compliance requirements regarding the security of the application or data stored. These concerns can be broadly categorised, in that an adversary or… Continue reading Penetration Testing Frequently Asked Questions
Why is penetration testing required?
What is Penetration Testing? Penetration testing, whether it be black box or white box, is a form of risk assessment that aims to identify cybersecurity vulnerabilities and risks within a system. Usually, security is considered a balancing act between confidentiality, integrity and availability. Confidentiality being the ability of the system to keep personal information secret.… Continue reading Why is penetration testing required?
Penetration Testing and Web Application Firewalls
A Web Application Firewall (WAF) is a defence-in-depth mitigation against common web attacks by monitoring and filtering HTTP traffic. WAFs work by analysing the plaintext content of HTTP messages between the client and server to determine if the given message is malicious. If it’s deemed to be malicious, the WAF stops the message from reaching… Continue reading Penetration Testing and Web Application Firewalls
White Box Penetration Testing
There are two main ways to conduct penetration testing: black box and white box. Both provide different approaches to the methodology and require different levels of interaction from the client. White box can often return more findings while improving the tester’s efficiency. We’ve already covered black box testing in the first part of this two-part… Continue reading White Box Penetration Testing
Black Box Penetration Testing
Penetration testing – or pen-testing as we colloquially call it – is a crucial component to a robust security programme in any organisation. As management, it’s critical you understand where pen-testing fits into your programme and what it can do for your organisation. Equally important is what it can’t do, and how the different “flavours”… Continue reading Black Box Penetration Testing
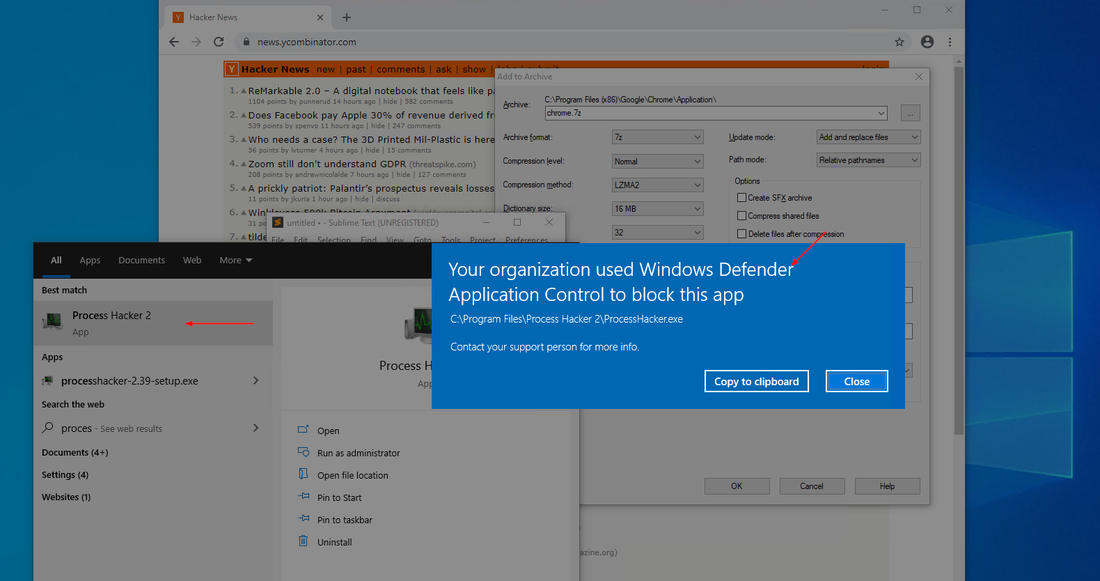
Upgrading from AppLocker to Windows Defender Application Control (WDAC)
Windows Defender Application Control (WDAC), formerly known as Device Guard, is a Microsoft Windows secure feature that restricts executable code, including scripts run by enlightened Windows script hosts, to those that conform to the device code integrity policy. WDAC prevents the execution, loading and running of unwanted or malicious code, drivers and scripts. WDAC also… Continue reading Upgrading from AppLocker to Windows Defender Application Control (WDAC)
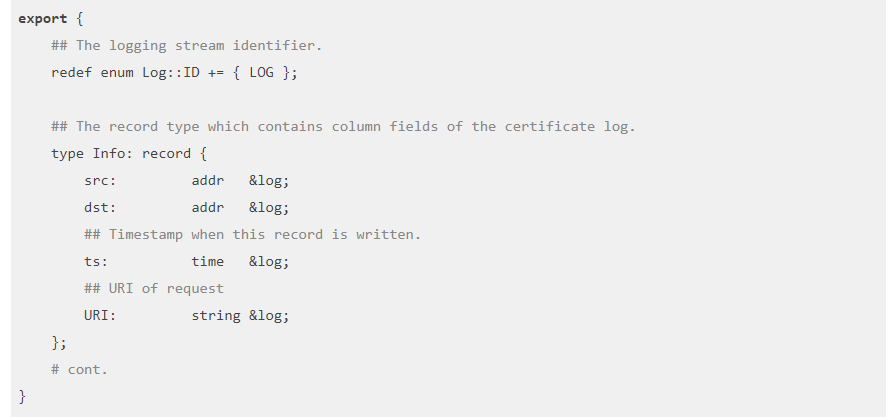
Using Zeek to detect exploitation of Citrix CVE-2019-19781
Using the tool Zeek, formally known as bro, is a high-level packet analysis program. It originally began development in the 1990s and has a long history. It does not directly intercept or modify traffic, rather it passively observes it and creates high-level network logs. It can be used in conjunction with a SIEM to allow… Continue reading Using Zeek to detect exploitation of Citrix CVE-2019-19781